Protecting Your Business Against Emerging Threats
In today’s interconnected world, cybersecurity is critical to safeguarding sensitive data, maintaining operational integrity, and protecting your business reputation. At Fortic Technologies, we provide detailed and actionable cybersecurity audit services to ensure your organization is resilient against modern cyber threats.
Our audits go beyond identifying vulnerabilities; we deliver strategic recommendations to enhance your security posture, ensure regulatory compliance, and help you adopt best practices in information security management.
Our Cybersecurity Audit Services
We offer a wide range of cybersecurity audits, tailored to meet your organization’s unique requirements:
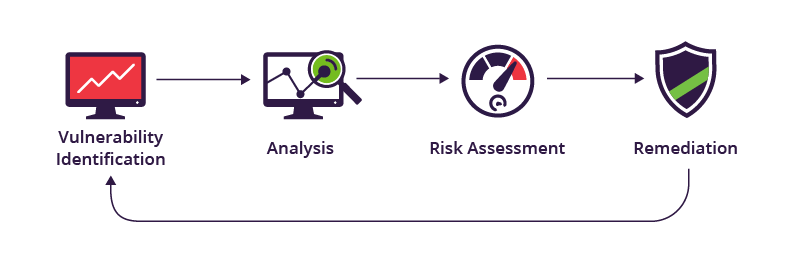
1. Vulnerability Assessments
Our experts conduct a detailed analysis of your IT infrastructure to identify potential weaknesses and gaps that cybercriminals could exploit.
Key Deliverables:
- Comprehensive assessment of systems, applications, and networks.
- Risk ratings to prioritize vulnerabilities based on severity.
- Tailored recommendations for mitigation and remediation.
- Optional ongoing monitoring solutions to track improvements.
2. Compliance Audits
Fortic Technologies helps your organization align with global and industry-specific cybersecurity regulations and standards. Non-compliance can lead to hefty penalties and damage to reputation, making this service vital for businesses handling sensitive data.
Standards and Regulations Supported:
- GDPR (General Data Protection Regulation)
- ISO/IEC 27001 (Information Security Management System)
- HIPAA (Health Insurance Portability and Accountability Act)
- PCI DSS (Payment Card Industry Data Security Standard)
- NIST Cybersecurity Framework
Key Deliverables:
- Gap analysis to identify compliance deficiencies.
- Development of a compliance roadmap tailored to your organization.
- Assistance with audit preparation and certification processes.
3. Cloud Security Audits
Ensure the security and compliance of your cloud environments. Whether you’re using AWS, Microsoft Azure, Google Cloud, or a hybrid solution, we assess configurations, access controls, and data protection mechanisms.

Key Deliverables:
- Evaluation of cloud provider settings and security configurations.
- Analysis of data storage, encryption, and access management policies.
- Mitigation strategies for cloud-specific risks like misconfigurations and unauthorized access.
- Recommendations for security improvements tailored to your cloud environment.
4. Network Security Audits
Your organization’s network is the backbone of your IT infrastructure. Our network security audits ensure that your systems are protected against unauthorized access, malware, and data breaches.
Key Deliverables:
- Thorough analysis of firewalls, routers, and switches for misconfigurations.
- Identification of unauthorized devices and shadow IT.
- Network traffic analysis to detect anomalies and potential threats.
- Recommendations for optimizing network security policies.
5. Information Security Audits
Assess your organization’s overall information security strategy, including policies, procedures, and controls. This audit focuses on how well your organization manages data confidentiality, integrity, and availability.
Key Deliverables:
- Review of data classification and handling policies.
- Evaluation of access control mechanisms and privilege management.
- Gap analysis of your security governance framework.
- Detailed recommendations for aligning with global best practices.
6. Incident Response Readiness Audits
Is your organization ready to respond to a cybersecurity incident? Our incident response readiness audit ensures you have the tools, processes, and people in place to detect, respond to, and recover from cyberattacks.
Key Deliverables:
- Review of current incident response plans and playbooks.
- Assessment of detection capabilities, including SIEM and threat monitoring tools.
- Recommendations for improving response times and coordination.
- Staff training suggestions to improve incident management capabilities.
7. Physical Security and Social Engineering Audits
Cybersecurity isn’t just about technology; it’s also about physical and human factors. Our audits extend to evaluating physical access controls and susceptibility to social engineering attacks.
Key Deliverables:
- Evaluation of physical security measures, including access to data centers and IT infrastructure.
- Analysis of organizational awareness and training in combating phishing, pretexting, and other social engineering techniques.
- Recommendations for improving physical and human-layer security defenses.
Why Choose Fortic Technologies for Cybersecurity Audits?
- Industry Expertise: Our certified experts have years of experience conducting audits across various industries.
- Tailored Solutions: We customize every audit to meet your organization’s specific risks and objectives.
- Comprehensive Reports: Receive detailed, easy-to-understand reports with clear, actionable recommendations.
- Focus on Improvement: We don’t just find problems—we work with you to develop solutions.
- Compliance Assistance: Ensure your organization is fully aligned with all relevant regulatory requirements.
Our Process
We follow a proven methodology to ensure every cybersecurity audit delivers maximum value:
- Initial Consultation: Understand your business, goals, and challenges.
- Planning and Scoping: Define the scope of the audit to focus on your priorities.
- Assessment and Analysis: Conduct a thorough review of systems, policies, and processes.
- Detailed Reporting: Deliver an in-depth report outlining findings, risk levels, and recommendations.
- Implementation Support: Provide guidance and support in implementing recommended improvements.
Industries We Serve
Our cybersecurity audits cater to organizations in diverse sectors, including:
- Financial Services
- Healthcare and Life Sciences
- Retail and E-Commerce
- Government and Public Sector
- Technology and SaaS Companies
- Manufacturing and Industrial